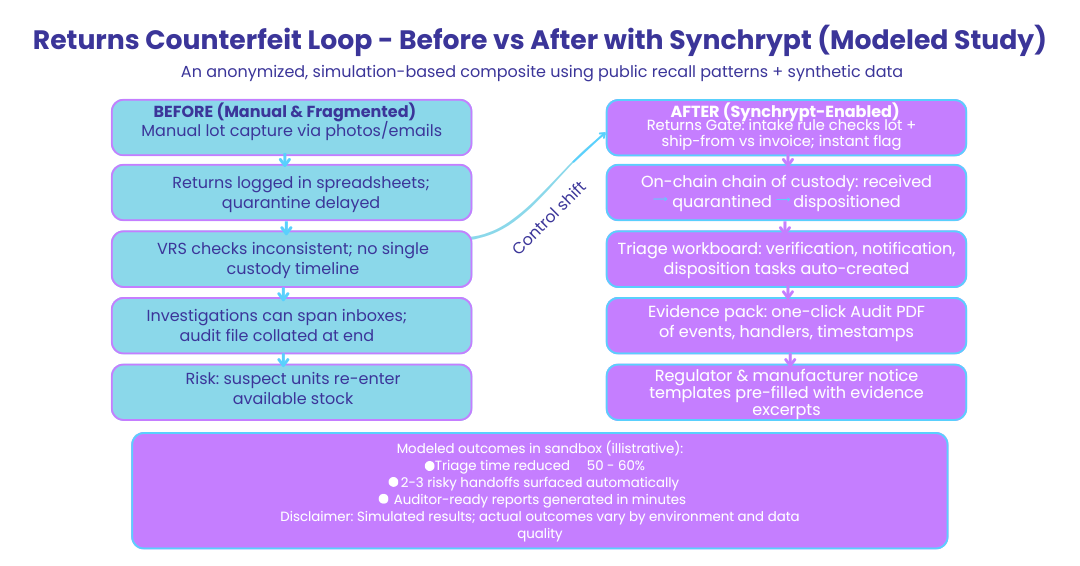
TL;DR: Using public recall patterns and synthetic data, we simulated how a mid-size pharma distributor could stop counterfeit re-entry through returns and 3PL handoffs. In our sandbox, Synchrypt helped cut triage time by ~50–60%, surfaced 2–3 risky handoffs, and generated an auditor-ready chain-of-custody report in minutes. These are modeled outcomes from a controlled environment; your results will vary.
Why we ran this simulation
Counterfeits rarely walk in the front door. They sneak in through returns, secondary wholesale deals, and opaque 3PL handoffs. Teams do their best with spreadsheets, email attachments, and spot checks—but evidence scatters and audits drag on.
We built a realistic scenario to answer a simple question: If you re-created a known recall pattern today, how quickly could you isolate, prove, and stop it?
How we built the case (transparent by design)
- Data sources: Public recall notices, DSCSA/EU FMD guidance, and open industry reports.
- Dataset: Synthetic lots, shipments, and invoices that mirror real-world volumes and error modes.
- Environment: Synchrypt sandbox with on-chain lot lineage, rule-based flagging, and exportable audit trails.
- Scope: U.S. distributor with one 3PL and two secondary wholesalers. Focus area: reverse logistics (returns).
Download our one-pager Method & Dataset for citations and modeling details.
The “Before” state we modeled
- Manual lot capture from photos/emails
- Returns intake recorded in sheets; quarantine not immediate
- VRS checks inconsistent; no single custody timeline
- Investigations span inboxes; audit file assembled at the end
Risk: Three suspect units slip through repackaging and re-enter available stock.
The “After” flow with Synchrypt (simulated)
- Returns Gate: On intake, a rule checks lot + ship-from vs invoice addresses → instant flag for mismatch patterns.
- Chain of Custody: Each movement writes an immutable event (received → quarantined → dispositioned).
- Triage Workboard: Auto-created case with tasks for verification, notification, and disposition.
- Evidence Pack: One-click Audit PDF exports timestamps, handlers, and actions taken.
- Regulator & MFR Notice: Pre-filled templates with custody excerpts included.
Modeled outcome (sandbox)
- Triage time ↓ ~50–60%
- 2–3 risky handoffs surfaced automatically
- Audit-ready report generated in minutes
These are simulated results for an illustrative scenario, not promises.
Quick walkthrough (screens you can show)
A. Flagged Return Intake
What to show: Return entry raising a “ship-from/invoice mismatch” + “duplicate lot in secondary channel” flags.
Alt text: “Return intake screen with automatic counterfeit risk flags.”
B. Lot Lineage Timeline
What to show: Scrollable custody chain with 3PL handoff nodes and timestamps.
Alt text: “On-chain lot lineage from receipt to disposition.”
C. Exported Audit PDF
What to show: Cover summary + event log with hash references.
Alt text: “Audit pack summarizing actions taken and custody evidence.”
D. Returns Gate Rule
What to show: Human-readable rule conditions; no code required.
Alt text: “Low-code rule that blocks risky returns and opens a triage case.”
Implementation blueprint (10-day pilot)
- Day 1–2: Map returns & 3PL steps; import 30 days of synthetic or redacted data (CSV ok).
- Day 3–5: Turn on 3 rules: Returns Gate, Address Mismatch, Duplicate Lot in Secondary Channel.
- Day 6–7: Run drill—intake 10 “suspect” returns; verify chain, export audit.
- Day 8–10: Adjust thresholds; align with SOP. Hand off the SOP addendum and training card.
No rip-and-replace: webhook/CSV adapters bridge your ERP/WMS while you pilot.
Limitations & what this doesn’t prove
- Real environments have data quality issues; flags may need tuning.
- We didn’t simulate every failure mode (e.g., deliberate label fraud at source).
- Performance depends on integration depth and team process.
That’s why we offer a guided, low-lift pilot before any production rollout.
Want the artifacts?
- Before/After Flow Map (PNG)
- Method & Dataset (1-pager PDF)
- SOP Addendum: “Suspect Product Intake in ≤15 minutes”
- Returns Gate Rule Template
FAQ
Is this a real customer?
No—this is an anonymized composite, modeled from public incidents and run in our sandbox. We publish our method so you can assess fit.
Why publish a simulation?
Because waiting for a crisis to prove a point helps no one. Simulations let teams see the control points and evidence trail before the stakes are high.
Can we try it with our data?
Yes. We can run a 10-day pilot using synthetic or redacted feeds.
About Synchrypt
Synchrypt helps pharma manufacturers, distributors, and 3PLs enforce verifiable chain of custody and block counterfeit re-entry—without adding operational drag. Evidence travels with the product, not in scattered files.